Device based authentication involves using a device to identify and verify a user’s identity. This type of authentication involves using a device, whether for its metadata or an app within the device. One example of device-based authentication is sending a one-time passcode via SMS. The user will be required to enter the one-time passcode which was sent over to the device via SMS to verify their identity. Similarly, users can use an authenticator app on their device instead of an SMS text to receive their one-time passcode. Another common example is the use of biometrics such as fingerprint recognition. Many banking apps require users to verify their identity via fingerprint recognition before being able to fully access all the banking app’s services.
These methods can offer intuitive and seamless experiences, especially if you are already on your phone and do not require switching devices; such as attempting to log into your computer but switching to your phone to obtain the one-time passcodes. However, device-based authentication is not as secure compared to other authentication methods.
Issues with Device Based Authentication
Device based authentication does not specifically verify that the current person who has possession of the device is who they claim to be. It only verifies that the person has access to the device. That is, the person knows the PIN or password to unlock the device and open the SMS or authenticator app to reveal the one-time passcodes. Some devices may also have multiple fingerprints from different people registered. They may be sharing the device with their partner or friend, which greatly compromises their security and privacy.
Device based authentication can also be easily compromised in the event of a stolen device. Fraudsters today use a multitude of sophisticated attacks to brute force their way into a device. These fraudsters can easily bypass or decipher security PINs and passwords. Once unlocked, the fraudsters will have access to the victim’s personally identifiable information stored on the device. Adding in the fact that users tend to never log out of their apps, fraudsters can conduct account takeovers with ease.
Voice Biometrics, An Alternative Option To Device Based Authentication
To mitigate the risks associated with device based authentication, solution providers can integrate voice biometrics for more secure and frictionless experience.
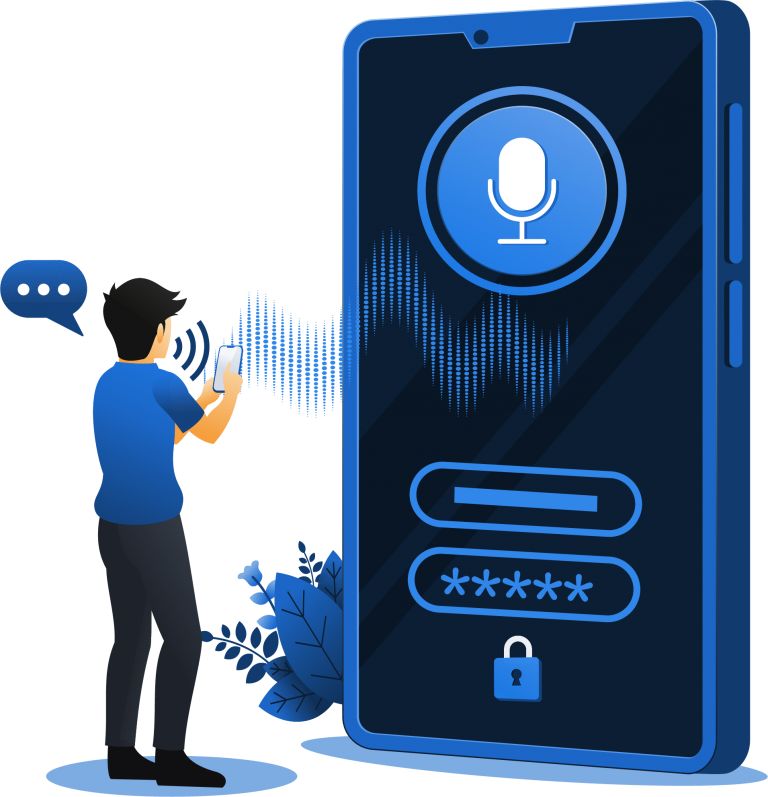
What makes voice biometrics more secure than other methods is that the voiceprints are not required to be stored on the device, unlike some fingerprint recognition systems. Voiceprints are stored behind the organization’s firewall and are stored separately from voice files. This means that voiceprints are not tied to the device itself and contain no personally identifiable information.
Voice biometrics can be used as an additional, step-up authentication method. It can also be used to completely replace existing authentication methods. For example, a user can be asked to verify their identity with a PIN and then followed up with a voice verification attempt by them saying their account number or phone number. This offers a complete multi-factor authentication experience as the user provides something they know (PIN), something they have (device), and something they are (voiceprint).
Voiceprints are also difficult to spoof, especially with Auraya’s voice biometric technology. With mimicked and synthetic voice detection, fraudsters attempting to defraud the system while using the victim’s device will struggle. Using recorded playback attacks will also not work as the system can thwart these attacks with random phrase challenges.